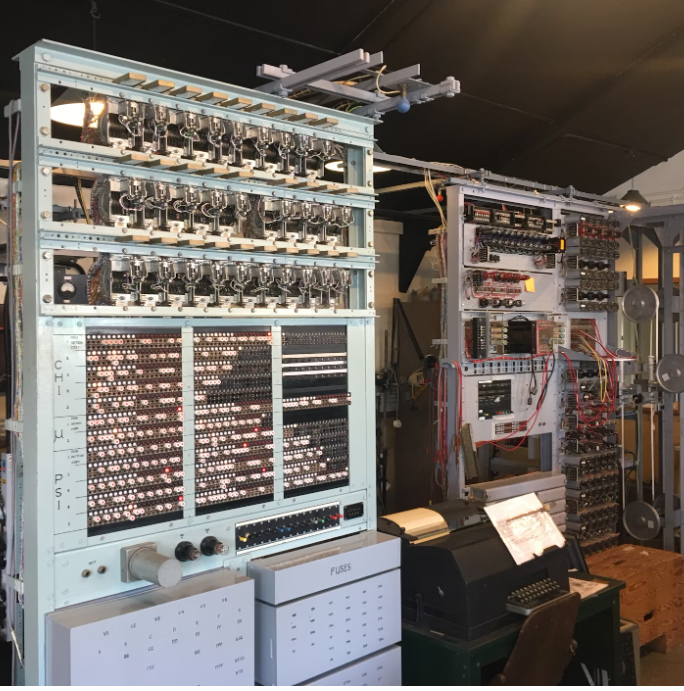
The global rollout of 5G technology is revolutionizing connectivity, offering ultra-fast speeds, lower latency, and increased network capacity. This next-generation wireless technology is laying the foundation for smart cities, autonomous vehicles, and IoT-driven industries, creating a more interconnected world. However, despite its rapid expansion, several challenges hinder its full-scale implementation.
Current Trends in 5G Adoption
Rapid Expansion in Developed Nations
Countries such as the United States, South Korea, China, and Japan are leading the way in 5G deployment. Major telecom providers like Verizon, AT&T, Huawei, and Ericsson are heavily investing in infrastructure, ensuring rapid expansion in urban areas. These nations are experiencing high demand for 5G connectivity, which is driving innovation in mobile networks, smart devices, and industrial applications. While developing nations like India, Brazil, and regions in Africa are gradually adopting 5G networks, the rollout is slower due to infrastructure limitations and high deployment costs. Governments and telecom providers in these countries are forming strategic partnerships to speed up 5G adoption, ensuring digital transformation reaches both urban and rural communities.
Enterprise Adoption Across Industries
Businesses across various industries are harnessing the power of 5G technology to enhance operations. Healthcare, manufacturing, and autonomous transportation are seeing significant advancements due to high-speed, low-latency networks. The healthcare sector is benefiting from 5G-enabled remote surgeries, while manufacturers are implementing smart factories with real-time automation. Autonomous vehicles, AI-driven logistics, and connected industrial IoT devices are all thriving on 5G connectivity.
5G-Powered Smart Cities and IoT
The rise of smart cities is closely linked to 5G technology, as real-time traffic management, smart grids, and enhanced public safety systems become more efficient. Additionally, the Internet of Things (IoT) is heavily reliant on 5G networks, enabling seamless connectivity for smart home devices, industrial sensors, and automated infrastructure.
Challenges Hindering 5G Implementation
High Infrastructure Costs
One of the most significant barriers to 5G implementation is the high cost of infrastructure. Deploying fiber-optic cables, small cell towers, and advanced base stations requires massive investment, making it challenging for rural and underdeveloped regions to fully embrace 5G networks.
Regulatory and Spectrum Allocation Issues
Governments worldwide are struggling with spectrum allocation and regulation, causing delays in 5G deployment. Licensing fees, spectrum availability, and geopolitical tensions between major tech powers have further complicated the adoption process. Countries that lack a clear 5G regulatory framework face difficulties in rolling out networks efficiently.
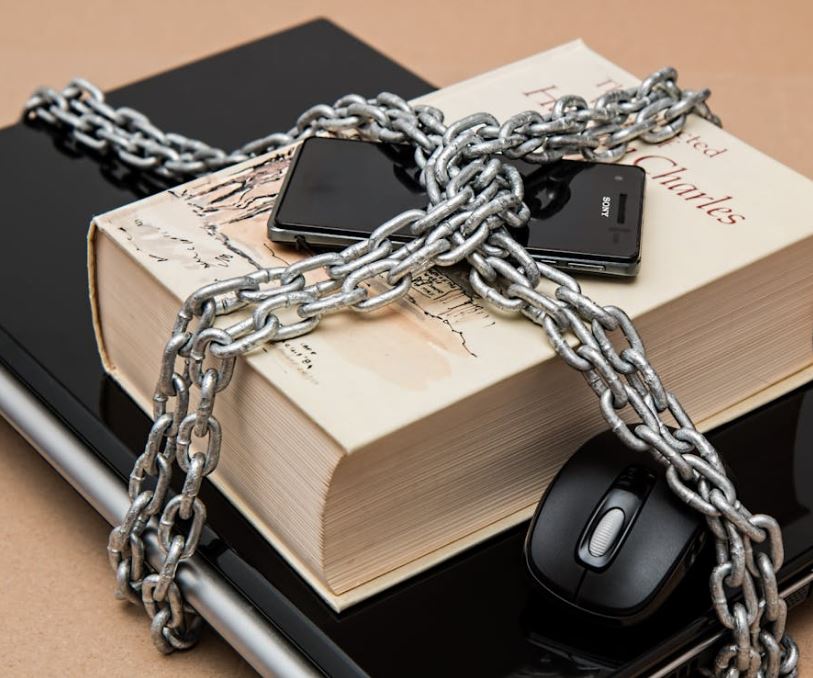
Cybersecurity and Privacy Risks
With an increased number of 5G-enabled devices, the risk of cybersecurity threats and hacking has also grown. Data privacy concerns, network vulnerabilities, and potential cyberattacks are some of the biggest challenges facing 5G adoption. Telecom providers and cybersecurity firms are working to implement stronger security measures to protect users and businesses.
Device Compatibility and Consumer Adoption
Although 5G-enabled smartphones, tablets, and IoT devices are becoming more available, many consumers still use 4G LTE technology, delaying mass adoption. Additionally, the cost of upgrading to 5G-compatible hardware remains a concern, especially in price-sensitive markets. Until devices become more affordable, consumer adoption will continue to be slower than expected.
Environmental and Health Concerns
The rapid expansion of 5G networks has raised questions about radiation exposure and potential health risks. While scientific research is ongoing, concerns remain about the long-term effects of increased electromagnetic frequency (EMF) exposure. Additionally, 5G infrastructure requires significant energy consumption, raising environmental concerns regarding sustainability.
The Future of 5G Technology
Despite the challenges, the future of 5G connectivity remains promising. As governments, telecom providers, and enterprises collaborate to address infrastructure costs, security concerns, and regulatory hurdles, the world moves closer to widespread 5G adoption. Continued investment in 5G infrastructure, cybersecurity advancements, and cost-efficient devices will accelerate the transition to a more connected and technologically advanced society.
The journey toward full-scale 5G implementation is not without obstacles, but the benefits far outweigh the challenges. Over the coming years, 5G networks will continue to reshape industries, improve global connectivity, and pave the way for a smarter, faster, and more efficient digital world.


 Personal Finance1 week ago
Personal Finance1 week ago
 Blog Post1 week ago
Blog Post1 week ago
 Economics6 days ago
Economics6 days ago
 Economics1 week ago
Economics1 week ago
 Accounting6 days ago
Accounting6 days ago
 Personal Finance1 week ago
Personal Finance1 week ago
 Economics6 days ago
Economics6 days ago
 Personal Finance6 days ago
Personal Finance6 days ago